Enhancing Security: NIST CSF/ISO 27001 Assessment
Case Study: How refreshing a fast-paced technology company’s Security Scorecard lead improved adherence to NIST CSF 2 and ISO 27001
Introduction: In today’s lightning fast digital ecosystem, technological advancement brings with it an ever growing array of cybersecurity threats. For a leading technology company in Palo Alto, California, this has presented an ongoing challenge to assess their security posture in order to safeguard their assets and maintain the trust of their stakeholders. Recognizing this challenge, the business embraced a proactive approach to cybersecurity and made the decision to have an updated security assessment performed.
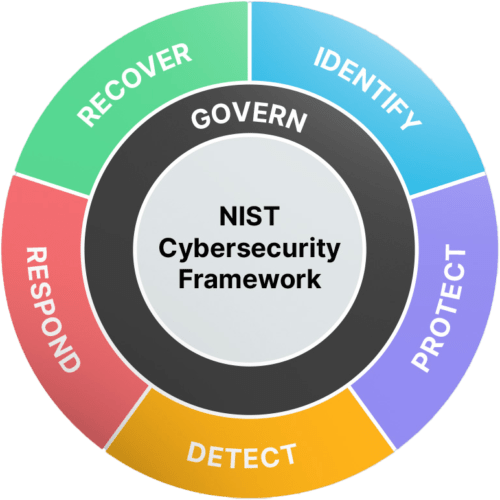
For a period of eight weeks, the Infoedge Team reviewed the previous ISO 27001 and NIST CSF assessment. We then conducted our own evaluation of their controls and mandatory requirements, analyzing each category and domain. We crafted a comprehensive assessment report, highlighting average maturity levels and showcasing the improvements in a board-friendly security scorecard. Our efforts continued as we documented areas for improvements and summarized observations in an executive report that adhered to our established “scorecards” approach.
Assessment: We collaborated closely with the software company and its C-level executives, and during this time, we reviewed the company’s security controls, documentation and security practices. Building on previous evaluations, we reviewed security controls, documentation, and security practices. Leveraging the ISO 27001 and NIST CSF standards, we were able to analyze each category and domain, mapping out the strengths and weaknesses.
Results: The culmination of the assessment process gave valuable insights into the company’s security posture. Through detailed reports and user friendly scorecards, we highlighted areas of excellence and identified areas that needed enhancement. From improving risk management practices to updating security training programs, the recommendations provided a roadmap to assist the business in improving its security posture.
Scorecard: We updated the security scorecard to assess how well the company’s defenses are working. These scorecards not only assessed compliance with industry standards, but also measured the functionality of security measures in place. With this information the company could prioritize resources effectively, mitigating risks and proactively addressing emerging threats.
Conclusion: By embracing a proactive approach to security, the business can now more effectively navigate their digital landscape with confidence. The recent refinements to the scorecard significantly improved its credibility and effectiveness, lending greater authority to its findings and recommendations. Presenting these insights to the Board of Directors was an important step, and they were well received. The refined scorecard, along with the updated outputs, clearly highlighted both the areas of significant progress and those needing improvement. This reaffirmed the importance of their ongoing efforts to strengthen their security measures.